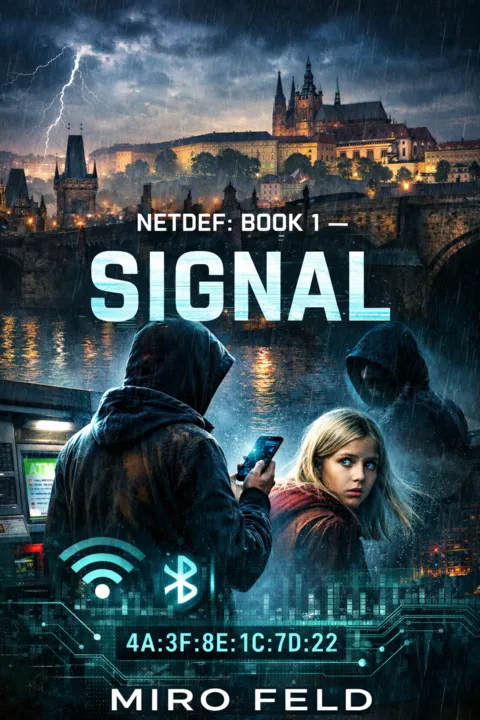

Z.R.A.K.: Signal
Two Prague teenagers detect the same crime from opposite ends — a fake hotspot, a hidden skimmer, a stranger following too closely. When a single device address connects their investigations, they realise they've stumbled onto something far bigger.
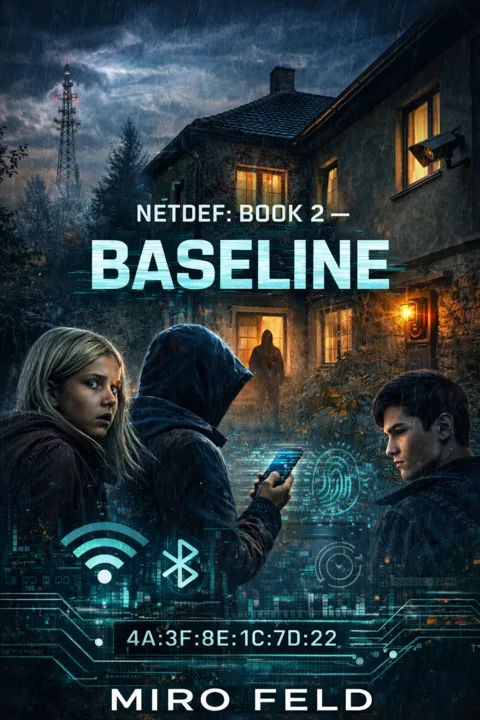

Z.R.A.K.: Baseline
Someone is poisoning the WiFi at Prague's neighbourhood cafes. Not fake networks — real ones. The password works, the encryption is real, and the attack lives inside the trust. To prove it, the group must learn what “normal broken” looks like.
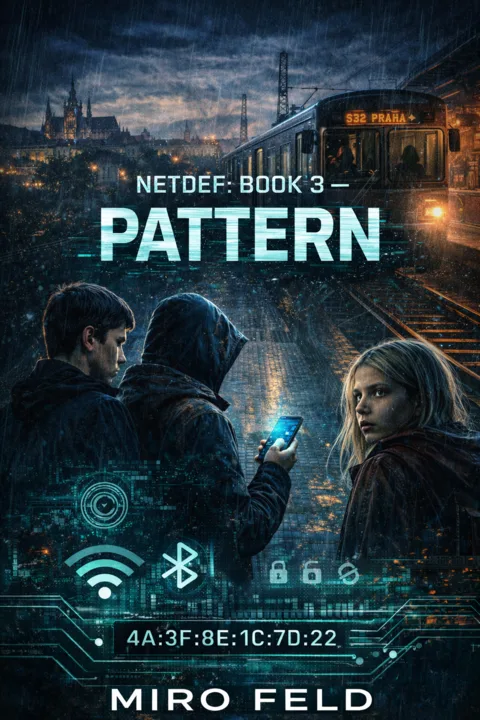

Z.R.A.K.: Pattern
A classmate's mother keeps sending invoices she didn't write. Every password changed, every security feature enabled — it keeps happening. The group investigates and finds a familiar device. They think they know what they're looking at. They're wrong.
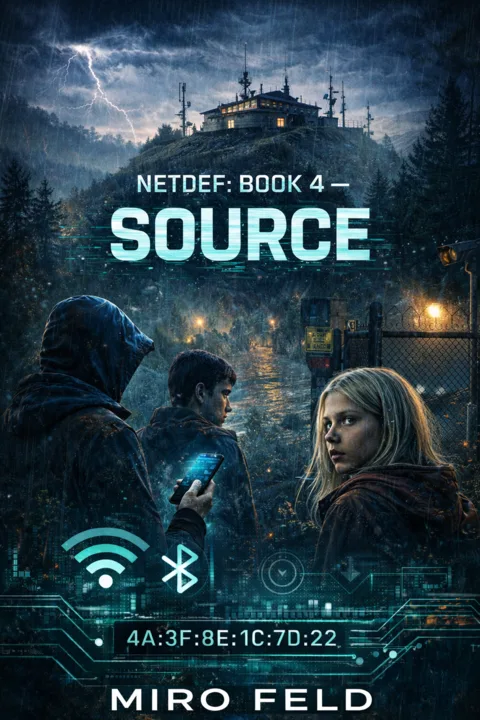

Z.R.A.K.: Source
Unmarked wireless devices appear in utility closets across Prague. No one claims them. No one knows who installed them. This time there is no crime in progress — just small white boxes and the hardest question: when is your part finished?

Z.R.A.K.: Trace
The case is in the hands of the police. A photograph of a fractal antenna travels from Prague to Brno — and is recognised. Not from the literature. From a different device, in a different case. Some answers arrive slowly. Some may never arrive at all.
Signal Lost
A disgraced signals intelligence specialist picks up an impossible Bluetooth pulse — a faint, repeating heartbeat from beneath an abandoned garage complex where no signal should exist. A technically authentic techno-thriller where noise means safety, silence means danger, and the most terrifying thing is a number dropping toward zero.

Z.R.A.K. Field Stories: Wireless Recon
135 technically authentic short stories spanning WiFi detection, network recon, counter-surveillance, and RF signal analysis. From a mountain rescue station in the Bieszczady to a co-working space in Mumbai — ordinary people discover extraordinary threats hiding in the radio waves around them. Fiction that teaches. Suspense that educates.
Z.R.A.K. Field Stories: Active Defense
136 new stories that go deeper — incident response, physical counter-surveillance, advanced field recon, and active defense. Skimmer hunts, rogue cell tower takedowns, BLE relay attacks, forensic evidence for courtrooms. If Book 1 taught you to see the threats, Book 2 teaches you to fight back.